
KYC (Know Your Customer) is an important process for cryptocurrency users in Ukraine, because it provides security and helps prevent fraud. In this article we will look at what KYC is, how it works in the crypto sphere and why it is important to follow verification procedures.
- KYC is not just a formality, but a necessary process to confirm identity and minimize risks.
- Verification levels affect functionality and transaction limits.
- Data protection and two‑factor authentication should be mandatory during verification.
- Several platforms offer different approaches to KYC, from strict to flexible.
- Keep correspondence with support in case of document rejection and request explanations.
What is KYC: concise and clear
KYC is a client check that establishes their identity and minimizes the risks of money laundering or fraud. The process includes collecting documents, verifying data and performing a risk assessment.
When to choose a service that emphasizes KYC: if you plan to work with fiat or large amounts. If you prioritize privacy: choose services with a clear data retention policy or consider decentralized identity solutions.
What the basic definition includes
- Identification — confirmation of name, date of birth and the document.
- Verification — confirmation that the document belongs to you (selfie, biometrics).
- Risk assessment — checking sanctions, PEP lists, and source of funds.
Unexpected note
KYC sometimes acts not only as a regulatory burden but also as a trust signal — a platform with transparent verification often attracts serious counterparties and reduces fraud risk.
KYC in crypto: how it works in the crypto space
Crypto KYC means applying verification standards within the cryptocurrency ecosystem — from exchanges to fiat gateways; different services require different amounts of data.
When to use a centralized exchange: if you need simple fiat buy/sell and support for payment cards. If you want anonymous trading, consider a DEX for crypto‑only operations, but remember risks related to liquidity and smart contracts.
What distinguishes crypto implementation of KYC
- Centralized exchanges and brokers: usually require full verification for fiat operations and withdrawals.
- P2P platforms: may have partial or flexible verification depending on the payment method.
- DEX and smart contracts: often do not require centralized KYC, but their fiat gateways do.
PEP and sanctions checks
PEP screening is a mandatory check for politically exposed persons. Sanctions filters verify compliance with international lists. The platform must document the procedures for these checks.
KYC verification — step by step
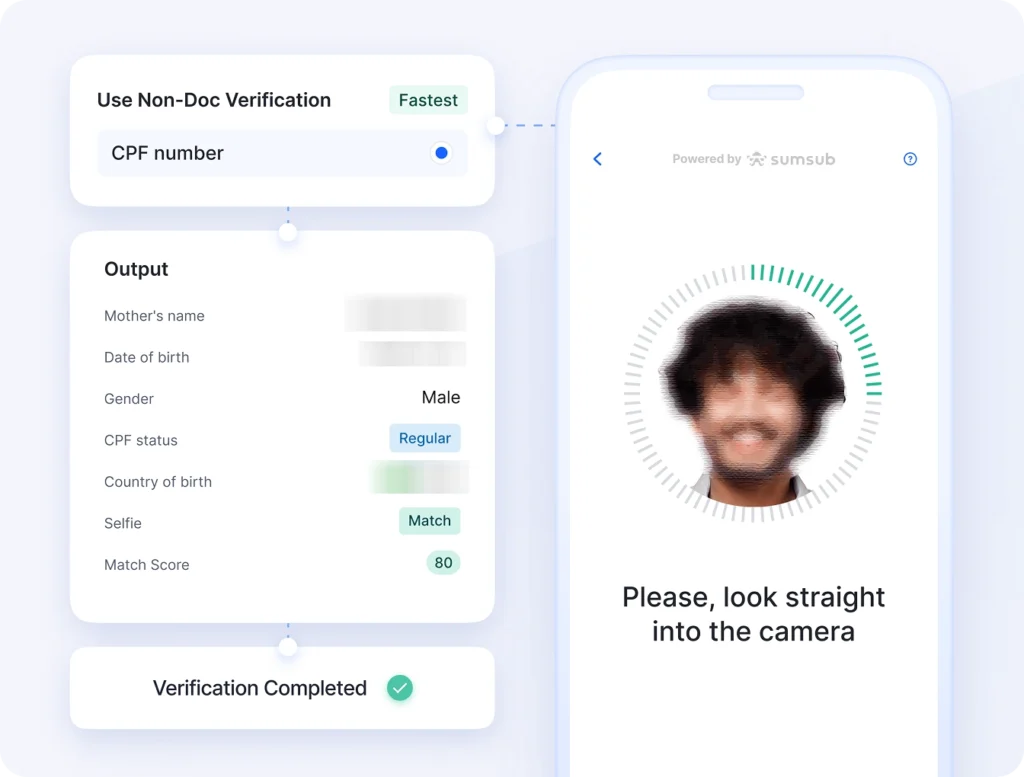
KYC verification is a practical set of actions from uploading photos to confirming address; the process is usually split into levels.
When to raise your verification level: if you plan to withdraw large amounts or use fiat. If your documents were rejected: check photo quality, file format and name/date consistency, then contact support.
Procedure steps
- Account registration: email and phone (basic level).
- Filling out the profile: full name, date of birth, country of residence.
- Uploading a document: passport or ID; photo format and clarity must meet requirements.
- Selfie with the document or live video (liveness detection) to confirm you are the document owner.
- Address confirmation: utility bill or bank statement with date and address.
- Additional requests: proof of source of funds — contracts, statements, declarations.
- PEP and sanctions screening; if positive, additional requests from compliance may follow.
- Receiving verified status and access to extended features/limits.
Process speed
Automated services — minutes; manual review — from several hours to a few days.
Tips for a smooth verification
- Photograph documents in good lighting; avoid glare.
- Use official formats PDF/PNG/JPEG, do not crop critical parts of the document.
- If the platform asks you to redact unnecessary fields — do so only within permitted limits.
Identity verification: methods, technologies and timelines
Identity verification includes OCR, biometrics and manual review; modern solutions combine several methods for accuracy.
When to demand only basic verification: for small operations and well‑known services. If you operate significant amounts: choose services with multi‑level verification and data storage compliant with GDPR and Ukrainian law.
Decoding complex terms
- OCR (Optical Character Recognition): technology that recognizes text on document photos — the first stage of automated processing.
- Liveness detection: a check that the user in front of the camera is live to prevent use of photos or videos.
- PEP screening: automatic comparison with politically exposed person databases.
- Sanctions filter: checks against international sanctions lists.
- Biometric trace: unique facial or behavioral characteristics used for authentication.
- KYC orchestration: the process of coordinating multiple verification providers into a single logic.
KYC risks and how to minimize them
The main risks are personal data leaks, false rejections and phishing attacks; they can be minimized by technical and procedural measures.
When a platform requires more data than you expected: ask for an explanation and the data retention policy. If you suspect a data leak, change passwords, disable 2FA and report it to the platform and the regulator.
Main risks and protection methods
- Data leaks: submit documents only over HTTPS; check the service’s reputation.
- False positives (incorrect rejections): keep copies of documents and contact support.
- Phishing: verify the domain, do not follow suspicious links.
- Excessive sharing with third parties: request a list of external providers.
Practical tips for Ukrainian users
In short: verify the platform’s legitimacy, minimize the volume of data you share and enable additional account security.
When to choose a platform with local support: if you plan fiat operations through Ukrainian banks. If you often work with large amounts: prepare proof of source of funds in advance.
Recommendations for preparing for verification
- Check the privacy policy and support contact details.
- Send only the documents required; redact unnecessary elements.
- Use 2FA apps or hardware keys.
- Prepare address proof documents with date and address.
- Keep correspondence with support in case of disputes or incorrect rejections.
Comparison of platform types by KYC requirements
In short: different platforms apply different approaches to KYC — centralized services are usually stricter, DEXs are more liberal.
| Platform type | KYC requirement | Advantages | When suitable |
|---|---|---|---|
| Centralized exchange | Full KYC for fiat; basic for small amounts | Fast fiat operations, card support | Fiat trading, large volumes |
| Exchanger | Depends on the amount; often standard KYC | Simplicity of exchange, speed | Crypto/fiat exchange for beginner users |
| P2P platforms | Flexible: from no KYC to full KYC | Local payment methods, flexibility | Local sales/purchases without bank gateways |
| DEX / smart contracts | Usually without centralized KYC | More privacy, no intermediary | Pure crypto operations, technically prepared users |
Common verification mistakes and how to fix them
Mistakes can slow down the process; below are the most common ones and how to correct them.
- Blurry document photos — how to fix: take new photos in good lighting, without glare or shadows.
- Name mismatch between documents — how to fix: provide documents that confirm the name change.
- Using public Wi‑Fi during upload — how to fix: restart the process using home or mobile internet.
- Ignoring a request to confirm the source of funds — how to fix: prepare records documenting the origin of funds.
- Not saving correspondence with support — how to fix: take screenshots immediately and save copies with timestamps.
Glossary of terms
KYC
KYC (Know Your Customer) — the process of collecting and verifying a client’s personal data to confirm their identity and assess risk.
AML/CFT
AML/CFT — measures against money laundering and terrorist financing; KYC is a basic element of these measures.
OCR
OCR — optical character recognition technology for documents that speeds up automated processing.
Liveness detection
Liveness detection — a set of methods to confirm that the person in front of the camera is real.
PEP
PEP (Politically Exposed Person) — a politically exposed person for whom enhanced controls are applied.
Sanctions filter
Automatic checks against international sanctions lists that block interactions with certain persons or entities.
Biometric trace
Unique biometric characteristics used for authentication.
KYC orchestration
KYC orchestration — coordinating multiple providers and technologies into a single verification process.
FAQ
Is KYC required for small‑volume transactions?
It depends on the platform: some services allow basic operations without full verification, others require KYC even for small amounts.
Can you avoid KYC in cryptocurrency?
Partially: decentralized platforms allow trading without centralized verification, but access to fiat often requires KYC.
Is it safe to submit passport data online?
It is safe only if the platform uses HTTPS, has a transparent data retention policy and a good reputation.
What to do if verification was rejected?
Review the reasons for rejection, correct the errors, keep correspondence and resubmit the request.
Can my data be transferred abroad?
Yes, some providers transmit data to external verification services.
How to prepare documents to confirm an address?
Prepare official documents with your name, address and date that are not older than the platform’s requirement.
What is PEP screening and why is it important?
PEP screening is a check for politically exposed persons; it is important for managing the risk of corruption and money laundering.
Can I request deletion of my data after verification?
It depends on the platform’s policy; in many jurisdictions a user can request data deletion.
What alternatives to classic KYC exist?
Decentralized identifiers (DID) and verification via credit/banking APIs.
Does KYC affect privacy?
Yes — KYC increases control and transparency, but requires sharing sensitive data.
Conclusion: KYC is a necessary balance between security, legal compliance and user convenience. Check platforms, prepare documents, enable two‑factor authentication and keep evidence of correspondence.

